No products in the cart.
Blog
Everything You Need to Know Before You Buy Clone Cards in 2026
Everything You Need to Know Before You Buy Clone Cards in 2026
Intruducing Clone Cards
Clone cards are counterfeit payment cards created using stolen card data. They are typically used in financial fraud schemes and are illegal in most jurisdictions. This page explains what clone cards are, how the fraud works at a systems level, the risks involved, how they are detected, and how individuals and businesses can protect themselves. It is written for readers who want a clear, factual understanding of the topic, whether for awareness, compliance, cybersecurity, or fraud prevention.
What Are Clone Cards?
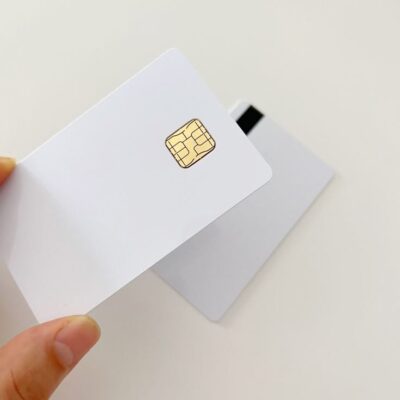
Clone cards refer to physical payment cards that have been fraudulently duplicated using stolen cardholder data. The cloned card typically contains copied magnetic stripe information from a legitimate debit or credit card. Criminals use this duplicated data to create counterfeit cards that can be used for unauthorized transactions.
Clone cards exist because payment systems historically relied on static data stored on magnetic stripes. If someone gains access to that data, often through skimming devices, data breaches, or compromised payment terminals, they can transfer it onto another card. The result is a counterfeit card that behaves like the original in certain payment environments.
The problem clone cards attempt to exploit is trust within payment networks. When a card is swiped, the terminal reads the magnetic stripe data and sends it to the issuing bank for authorization. If the data appears valid and the transaction fits normal patterns, it may be approved, even if the physical card is fraudulent.
Example:
A criminal installs a skimming device on a fuel pump. Card data from multiple customers is captured. That data is later written onto blank cards with magnetic stripes. Those counterfeit cards are then used to make purchases or withdraw funds until the fraud is detected.
Clone card activity is a form of payment fraud and is prosecuted as financial crime in most countries.
The Evolution and History of Clone Cards
Clone cards first appeared in the early 2000s when card-skimming became mainstream at ATMs and gas stations. As skimming devices advanced, so did card cloning software and techniques, eventually growing into sophisticated magnetic and chip cloning technologies.
By the 2010s, fraud rings were producing high-quality clone cards using EMV data copied via shimmers, POS interceptors, or social engineering attacks.
Today, clone cards are part of a vast underground network and are now being used in everything from penetration testing to undercover investigations, and even documentary journalism.
Authentic Clone Card: Are They Real?
High-quality clone cards, such as those found at TrustedBillsAndClones.com, are crafted using real magnetic stripe and EMV chip data, ensuring they function like the original cards. This means they can be used at ATMs, stores, or online (depending on the encoded data and method of use).
However, authenticity comes down to data quality, card construction, and encoding accuracy. Poorly cloned cards fail quickly, while professionally made clone cards are indistinguishable from real cards to most terminals.
Fun Fact: Clone cards from TrustedBillsAndClones.com come encoded, tested, and ready to use.
How Clone Card Fraud Works
Clone card fraud operates by exploiting weaknesses in payment authentication systems, particularly those relying on magnetic stripe technology.
At a system level, here’s what happens:
Data Capture: Card data is stolen through skimming devices, malware, or database breaches.
Data Encoding: The stolen data is transferred onto another card’s magnetic stripe.
Transaction Attempt: The cloned card is used at a terminal that accepts magnetic stripe transactions.
Authorization Check: The issuing bank verifies the account number, expiration date, and security code.
Approval or Decline: If no red flags appear, the transaction may be approved.
Explore our indept guide on how clone card Fraud works
Key Components Involved
Cardholder data (PAN, expiration date, CVV in some cases)
Magnetic stripe encoding format (Track 1 and Track 2 data)
Payment terminal compatibility
Issuing bank fraud detection systems
Card network authorization infrastructure
How Components Interact
When a card is swiped, the payment terminal reads track data and sends it through an acquiring bank to the card network (e.g., Visa, Mastercard). The issuing bank checks:
Account validity
Available credit or balance
Fraud risk signals
Transaction history
If the cloned card’s data matches the legitimate account and no unusual behavior is flagged, the transaction may proceed.
Modern chip-enabled EMV cards significantly reduce this risk because they generate dynamic authentication codes, which cannot be reused from stolen data.
Key Components That Affect Clone Card Fraud
1. Magnetic Stripe Technology
What it is:
A legacy payment technology storing static cardholder data.
Why it matters:
Static data can be copied and reused.
Impact:
High vulnerability to duplication compared to EMV chips.
Common misconception:
Many assume chip cards eliminate fraud entirely. They reduce cloning but do not eliminate all types of card fraud.
2. Skimming Devices
What they are:
Illicit devices placed on ATMs or point-of-sale terminals to capture card data.
Why they matter:
They enable large-scale data harvesting.
Impact:
Can compromise hundreds or thousands of cards before detection.
Misconception:
People often believe skimming only happens in remote locations. In practice, it has occurred in urban retail stores, restaurants, and fuel stations.
3. EMV Chip Adoption
What it is:
Chip-based authentication using dynamic cryptograms.
Why it matters:
Prevents replay attacks using static data.
Impact:
Countries with widespread EMV adoption have seen sharp declines in clone card fraud.
Misconception:
Some assume fallback to magnetic stripe is harmless. In reality, fallback transactions increase fraud risk.
4. Fraud Detection Algorithms
What they are:
Machine learning systems that flag suspicious transactions.
Why they matter:
They detect abnormal spending patterns.
Impact:
Rapid detection limits financial losses.
Misconception:
Fraud detection is not instant in all cases; some fraudulent transactions may succeed before intervention.
Types and Variations of Clone Card Fraud
While the core concept remains the same, there are variations in execution and targeting.
| Type | Description | Typical Target | Risk Level |
|---|---|---|---|
| ATM Cloning | Used to withdraw cash | Debit cards | High |
| Retail POS Cloning | Used for in-store purchases | Credit cards | Moderate to High |
| Cross-Border Usage | Used in regions with weaker chip enforcement | International cards | High |
| Fallback Exploitation | Magnetic stripe used when chip fails | Mixed | Moderate |
Each variation depends on payment infrastructure, regulatory environment, and fraud detection maturity.
How Clone Card Fraud Is Measured and Detected
Financial institutions track clone card fraud using several metrics:
Fraud rate (percentage of total transactions)
Fraud loss per card issued
False positive rate (legitimate transactions declined)
Chargeback volume
Geographic risk concentration
Detection Tools
Behavioral analytics
Transaction monitoring systems
Geolocation mismatch detection
Velocity checks (rapid transaction attempts)
EMV fallback monitoring
Benchmarks
In mature markets with strong EMV enforcement, counterfeit card fraud has declined significantly. However, fraud often shifts geographically to regions with weaker chip enforcement.
Limitations
Fraudsters adapt quickly.
Detection models can generate false positives.
Some fraud is only detected after customer reporting.
How to Prevent and Mitigate Clone Card Fraud
Prevention requires layered security across consumers, merchants, and financial institutions.
For Consumers
Use chip or contactless payments instead of swiping.
Inspect ATMs and fuel pumps for tampering.
Enable transaction alerts.
Monitor statements regularly.
Report suspicious charges immediately.
For Merchants
Disable magnetic stripe fallback where possible.
Regularly inspect terminals.
Implement PCI DSS compliance.
Train staff on tampering indicators.
Use encrypted point-to-point payment systems.
For Financial Institutions
Invest in real-time fraud monitoring.
Limit cross-border risk exposure.
Monitor fallback transactions.
Use adaptive authentication methods.
Each step reduces exposure by either limiting data theft or improving detection speed.
Real-World Examples and Use Cases
Example 1: Fuel Pump Skimming
A regional fuel chain discovered increased chargebacks linked to magnetic stripe transactions. Investigation revealed skimming devices installed inside pump enclosures. After upgrading to tamper-resistant hardware and enforcing chip-only payments, fraud losses declined substantially.
Lesson: Infrastructure matters. Physical security reduces digital fraud.
Example 2: Cross-Border Fraud Migration
After a country implemented full EMV chip enforcement, counterfeit fraud dropped domestically but increased in nearby regions without chip mandates.
Lesson: Fraud often migrates rather than disappears.
Clone Cards vs. Card-Not-Present Fraud
| Feature | Clone Cards | Card-Not-Present (CNP) Fraud |
|---|---|---|
| Requires physical card | Yes | No |
| Uses magnetic stripe | Often | No |
| Common channel | In-store/ATM | Online |
| EMV protection impact | High reduction | Limited effect |
| Fraud trend | Declining in chip markets | Increasing globally |
Clone cards involve physical duplication, whereas CNP fraud uses stolen card data for online transactions. As chip adoption increased, fraud shifted toward online channels.
Common Mistakes and Myths
Myth 1: Chip Cards Are Fraud-Proof
They reduce cloning but do not eliminate online fraud.
Myth 2: Small Transactions Are Harmless
Fraudsters often test small amounts before attempting larger withdrawals.
Myth 3: Only Tourists Are Targeted
While travelers can be vulnerable, domestic consumers are frequently affected.
Mistake: Ignoring Alerts
Delayed reporting increases financial losses and recovery complexity.
Edge Cases, Limitations, and Tradeoffs
Some regions still require magnetic stripe compatibility.
Disabling fallback may reduce convenience but increases security.
Fraud detection systems can block legitimate transactions.
Smaller merchants may struggle with upgrade costs.
Fraud prevention improvements often shift crime to new channels.
Security improvements rarely eliminate fraud entirely; they redistribute risk.
Why Clone Cards Are in High Demand
People seek clone cards for several reasons:
Privacy-Focused Transactions
Those who wish to make anonymous purchases.Penetration Testing & Research
Security professionals test ATM and POS security systems.Emergency Cash Withdrawals
Some use clone cards preloaded for travel or emergencies.Educational Training
Clone cards are used in cybercrime courses and security workshops.
Common Uses of Clone Cards
ATM cash withdrawals
In-store purchases at chip/mag stripe terminals
Online payments (with matching CVV data)
POS system testing
Accessing preloaded funds
Privacy-centered spending
Advantages of Using High-Quality Clone Cards
When you buy clone cards online from a reliable source, you enjoy several benefits:
Increased Privacy
Spend without linking your identity to the transaction.Real-Time Usability
Use at ATMs and stores without detection.Research & Testing Applications
Perfect for cybersecurity, IT research, or POS testing.Learning Tool
Learn how magstripes and chips work in real-world scenarios.
Where to Buy Clone Cards in the USA
Buying clone cards online can be risky, only use verified vendors that offer:
Encrypted communication
Discreet packaging
Real customer testimonials
Secure payment methods (BTC, USDT, etc.)
At TrustedBillsAndClones.com, you’ll find authentic clone cards with full track 1/2/3 data, delivered securely and quickly.

How to Buy Clone Cards Online
Visit our shop: Clone Cards for Sale
Select your desired clone card package (track 1, 2, 3)
Add to cart and proceed to secure checkout
Pay with crypto (Bitcoin or USDT recommended)
Receive shipping confirmation and tracking
All clone cards are tested before dispatch.
Discreet Delivery & Global Shipping on all Clone Cards
At TrustedBillsAndClones.com, we ship to the USA, UK, Canada, Australia, and more using stealth packaging and fully trackable methods. Your privacy is our priority.
No card or product branding
Vacuum-sealed envelopes
Tracking IDs are emailed instantly
24/7 Customer Support
Need help before or after your order? Our support team is available:
Live chat on TrustedBillsAndClones.com
Email ticketing within 24 hours
Order tracking and updates
FAQs: Clone Cards
Are clone cards illegal?
Yes. Manufacturing, distributing, or using cloned payment cards is illegal in most jurisdictions and considered financial fraud.
Can chip cards be cloned?
Chip data cannot be duplicated in the same way as magnetic stripe data. However, other types of fraud may still occur.
How do I know if my card was cloned?
Unexpected transactions, especially from unfamiliar locations, may indicate compromise.
Who is liable for clone card fraud?
Liability depends on jurisdiction and compliance standards, but consumers are often protected if fraud is reported promptly.
Is clone card fraud increasing?
In many EMV-enabled countries, clone card fraud has declined, but it remains present in regions with weaker chip enforcement.
What data is encoded on clone cards?
Track 1 and 2 (card number, name, expiry, CVV) and optionally Track 3.
Can I use clone cards online?
Yes, if the card includes CVV and matching billing data.
Are clone cards safe to use?
If used ethically and responsibly, they function as intended. We do not support illegal usage.
People Also Ask
How do clone cards work?
Are clone cards legal to use?
Can I withdraw money using clone cards?
What is the best site to buy clone cards?
Do clone cards include PIN codes?
Shop Now: Clone Cards for Sale
Explore the best selection of encoded clone cards for sale only at TrustedBillsAndClones.com. Each product is vetted, tested, and delivered with care.


AMAZING POST THANKS FOR SENDING THIS POST
I love what you guys tend to be up too. This sort of clever work and
exposure! Keep up the awesome works guys
I’ve added you guys to my personal blogroll.
Very quickly this site will be famous among all blog
visitors, due to it’s fastidious content
Undeniably imagine that which you said. Your favourite justification appeared to
be on the internet the simplest thing to take into account
of. I say to you, I certainly get irked even as folks consider issues that they
just don’t realize about. You managed to hit the nail
upon the highest as smartly as outlined out the whole thing without having side-effects , people can take a signal.
Will probably be again to get more. Thank you
Can you tell us more about this? I’d love to find out some additional information.
Hi there to all, how is everything, I think every one is getting more from this web page,
and your views are good for new viewers.
Your article helped me a lot, is there any more related content? Thanks!
Thanks for sharing. I read many of your blog posts, cool, your blog is very good.
Thanks for sharing. I read many of your blog posts, cool, your blog is very good.